Cloud Security Market Insights, 2032
The global cloud security market size was valued at USD 35.8 billion in 2022, and is projected to reach USD 125.8 billion by 2032, growing at a CAGR of 13.6% from 2023 to 2032.
The growing emergence of development security operations in the cloud environment, increasing number of cyber-attacks, growing reliance on cloud-based services, and increasing market for managed services, as these factors propel the growth of cloud security market. Furthermore, factors such as lack of awareness regarding cloud security and high navigation costs and stringent regulations are hampering the growth of cloud security market. Moreover, factors such as the development of cloud computing landscape and growth of mobile computing are providing an opportunity for cloud security industry expansion.

Cloud security protects cloud data, applications, and infrastructure from cyber-attacks and cyber threats. Business-critical apps and data are moving to reputable third-party cloud service providers (CSPs) as enterprise cloud usage increases. The majority of major CSPs include standard cybersecurity tools with monitoring and alerting features in their service offerings, but internal IT security staff may find that these tools do not cover all the bases, indicating that there are cybersecurity gaps between what the CSP offers and what the enterprise needs. Data loss and theft are now more likely as a result. Business executives are weighing the advantages of using cloud services with the level of data security risk their firms are willing to incur because no enterprise or CSP can completely eradicate security risks and vulnerabilities. It's crucial to implement the appropriate cloud security measures and rules.
The report focuses on growth prospects, restraints, and trends of the cloud security market analysis. The study provides Porter's five forces analysis to understand the impact of various factors, such as bargaining power of suppliers, competitive intensity of competitors, threat of new entrants, threat of substitutes, and bargaining power of buyers, in the cloud security industry.
Segment Review
The cloud security market is segmented on the basis of type, end-user, deployment, vertical, and region. In terms of type, the market is divided into cloud identity and access management, e-mail and web security, data loss prevention, cloud database security, network security, and cloud encryption. By end user, the market is bifurcated into large-scale enterprises and small & medium enterprises. Based on deployment, it is divided into public, private and hybrid. By vertical, the market is divided into healthcare, BFSI, IT & telecom, government agencies, retail, and others. On the basis of region, it is analyzed across in North America cloud security market, Europe, Asia-Pacific, and LAMEA.
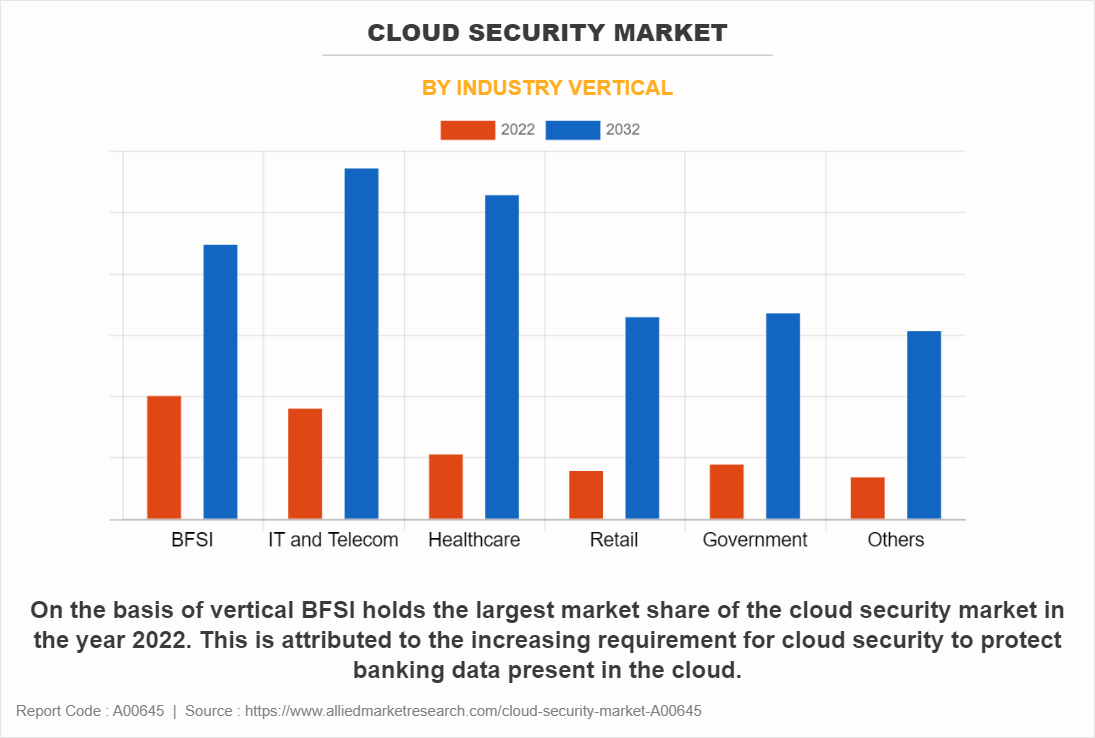
On the basis of vertical BFSI holds the largest market share of the cloud security market in the year 2022. This is attributed to the increasing requirement for cloud security to protect banking data present in the cloud. However, the healthcare market is expected to portray the largest CAGR of 17.7% from 2022 to 2032 and is projected to maintain its lead position during the forecast period. This is attributed again to the increasing need of cloud security to protect large amount healthcare data present in the cloud.
Based on region, North America held the highest market share in terms of revenue in 2022, accounting for more than two-fifths of the global cloud security market revenue, owing to the increasing demand and use of cloud technology by large number of key technological companies present in the region. However, the Asia-Pacific region is expected to witness the fastest CAGR of 16.6% from 2022 to 2032, and is likely to dominate the market during the forecast period, owing to the large number of technological start-ups growing in the region.
The report analyzes the profiles of key players operating in the cloud security market such as Fortinet Inc., Sophos Ltd., Cloudflare Inc., Tenable Inc., BMC Software Inc., Broadcom Corporation, Cisco Systems Inc., IBM Corporation, Trend Micro Inc., and Watchguard Technologies Inc. These players have adopted various strategies to increase their market penetration and strengthen their position in the market.
Top Impacting Factors
Growing Emergence of DevSecOps in the Cloud Environment
The rise of DevSecOps in the cloud environment is driving the growth of cloud security market. DevSecOps in cloud security is becoming a key advantage to the mass adoption of cloud computing. DevSecOps has resulted in more secure applications in the cloud by addressing, extracting and fixing vulnerabilities at the development stage.
Furthermore, DevSecOps teams keep an eye on the security of products as they are developed and released. They have different responsibilities such as process monitoring, risk analysis collection, automating security measures, and incident management. It helps businesses adopt efficient risk management for cloud security, addressing cloud security issues. Companies using the cloud occasionally need to modify their codes multiple times per day. Following outdated security models does not help in this situation as they are not appropriate for quick delivery cycles.
However, DevSecOps technology assists security teams in regularly checking for vulnerabilities and improving the quality assurance procedure. The technology helps in analyzing code that keeps software healthy throughout the cloud migration process, even while moving to the cloud. DevSecOps technology helps in automating testing. Automated tests streamline the entire testing process by carrying out repeatable tests, logging outcomes, and providing the team with feedback in a rapid manner. By removing coding errors, running automated tests across the entire development process increases overall efficiency. The overall cloud migration procedure can be streamlined as a result, making it simpler to move more resources to the cloud.
For instance, Amazon Web Services (AWS) security hub is a DevSecOps-based cloud security posture management service that performs best security practice checks, aggregates alerts and enables automated remediation. Therefore, development security operations technology will drive the cloud security market growth for the forecast period.
Increasing Number of Cyber-attacks
Increase in digitalization is simultaneously increasing the risk of data security and cyber-attacks and therefore driving the growth of cloud security market. The growing production of digital material and the lack of security measures to safeguard corporate and financial data has resulted in a large number of data theft cases in the past recent years. For instance, Techopedia stated 493.33 million ransomware attacks were detected by organizations in 2022. The most targeted industries are BFSI, IT & telecom, and retail. Therefore, the market would experience faster growth in the future due to the rising number of cyber-attacks and data breach incidents.
Growing Reliance on Cloud-based Services
The rising reliance on the cloud for storage and other applications is the outcome of rising use of cloud services across numerous industries. The main influencing reasons for the adoption of cloud security solutions are the rising number of internet users and the expanding use of cloud services. The development of online commerce through time would emphasize the importance of this issue. Therefore, all these factors are responsible for escalating the growth of cloud security market.
Increasing Market for Managed Security Services
Due to its flexibility to tailor the set of services to requirements, cloud-based managed security services are anticipated to see increased market acceptance. The idea of managed security service provides defense against intrusions and cyber-attacks and includes managed two-factor authentication, content filtering, next-generation firewalls, and even security consulting. Market participants should benefit from several opportunities due to this. The strategy used for product launches dominates the market.
The market for cloud security has expanded due to the rising popularity of cloud-based services and their varied applications across a variety of industries, including healthcare, BFSI, IT & telecom, government, and retail. For instance, Gartner stated the managed services market grew by 15.8% in US dollars to reach $16.98 billion in revenue in 2022. To diversify their product offerings and expand their portfolios, market vendors provide specialized and unique goods. Therefore, all these factors will drive the market growth for the cloud security market for the forecast period.
Regional Insights
North America:
North America is the leading region in the cloud security market, primarily driven by the high adoption rates of cloud computing and stringent data protection regulations. The U.S., in particular, has a strong presence of major cloud security providers and a robust regulatory environment, including regulations such as the Health Insurance Portability and Accountability Act (HIPAA) and the Sarbanes-Oxley Act. The region’s focus on advanced threat detection, compliance, and data privacy drives significant investment in cloud security solutions. Additionally, increasing cyber threats and the shift to remote work continue to fuel the demand for comprehensive cloud security services in North America.
Europe:
Europe is a significant market for cloud security, influenced by the stringent data privacy regulations under the General Data Protection Regulation (GDPR) and other national regulations. Countries such as the UK, Germany, and France are leading the adoption of cloud security solutions to ensure compliance and protect sensitive data. The region’s emphasis on maintaining high standards of data protection and mitigating cyber threats drives demand for advanced cloud security solutions. The rise of digital transformation initiatives and increased cyberattacks across various industries further contribute to the growing need for robust cloud security measures in Europe.
Asia-Pacific:
The Asia-Pacific region is experiencing rapid growth in the cloud security market, driven by the region's expanding digital infrastructure and increasing cloud adoption across countries like China, India, Japan, and Australia. The rise in cyber threats and the need to protect sensitive data are major factors driving the demand for cloud security solutions. Additionally, government initiatives promoting cybersecurity and the growing awareness of data privacy are contributing to market growth. The proliferation of digital services and the increasing use of cloud-based applications in sectors such as finance, healthcare, and e-commerce further support the expansion of cloud security in Asia-Pacific.
Latin America:
Latin America is gradually adopting cloud security solutions, with growing interest in countries like Brazil and Mexico. The region is witnessing an increase in cloud computing adoption, driven by digital transformation efforts and the need for enhanced data protection. While cloud security adoption is still developing compared to other regions, the rising incidence of cyberattacks and regulatory pressures are prompting organizations to invest in cloud security solutions. The market growth is supported by the increasing awareness of cybersecurity threats and the need for compliance with international data protection standards.
Middle East and Africa:
The Middle East and Africa (MEA) region is seeing growing investments in cloud security, particularly in the Gulf Cooperation Council (GCC) countries like the UAE, Saudi Arabia, and Qatar. These countries are focusing on strengthening their cybersecurity frameworks and protecting critical infrastructure from cyber threats. In Africa, cloud security adoption is in the early stages but is gaining traction with the increasing deployment of cloud services and digital transformation initiatives. The region’s growing concern about data breaches and cyberattacks, coupled with government efforts to enhance cybersecurity, is driving the demand for cloud security solutions across MEA. However, challenges related to infrastructure and connectivity may affect the pace of adoption in some areas.
Market Landscape and Trends
The expansion of cloud security market is driven by various trends. market is witnessing a growing market size due to increasing adoption of cloud technology across businesses of all sizes. Furthermore, many major players are present in the market that offer cloud security solutions. Cloud security solutions cover a variety of areas including data encryption, identity and access management, threat detection and response compliance management and others. Government and regulatory bodies are imposing stricter regulations regarding data privacy and security. This is forcing businesses to invest in cloud security to comply with the regulations and avoid hefty fines.
The zero trust model is becoming a popular option for cloud security as it requires strict identity verification for anybody to access resources on private network. In addition, artificial intelligence and machine learning technologies are being integrated into cloud security solution to enhance threat detection capabilities. These technologies can improve analyze patterns, detect anomalies, and threat response in real-time.
Key Industry Development
Recent Product Launches in cloud Security Market
In July 2023, Sophos Ltd. launched Sophos managed detection and response (MDR) for Microsoft defender. A completely managed service that offers businesses employing Microsoft Security the most powerful threat response capabilities available in the market. In order to defend against data breaches, ransomware, and other active adversary cyberattacks, Sophos MDR for Microsoft Defender adds a crucial layer of 24/7 protection across the Microsoft Security suite of endpoint, SIEM, identity, cloud, and other technologies.
In September 2023, Cloudflare Inc. launched Cloudflare One Data Protection Suite, a unified collection of cutting-edge security tools made to safeguard data in every environment, including online, SaaS, and private applications. Customers can streamline compliance in the cloud, reduce data exposure and source code loss, secure developer and AI environments from a single platform due to Cloudflare's Security Service Edge (SSE), which is powered by Cloudflare.
Recent Partnerships in Cloud Security Market
In May 2020, BMC software partnered with Rah Infotech, the specialty technology distributor of mission critical technology solutions including network and cybersecurity, data management, disaster recovery and cloud to offer a range of data analytics, service assurance and automation solutions to businesses.
In April 2021, Broadcom Inc. collaborated with Google Cloud to increase integration of cloud services and speed up innovation inside Broadcom core software businesses. In accordance with this partnership, Broadcom will make its enterprise operations and security software suite available on Google Cloud, allowing companies to implement its security, DevOps, and other solutions on the reliable, worldwide infrastructure of Google Cloud.
Key Benefits for Stakeholders
This report provides a quantitative analysis of the market segments, current trends, estimations, and dynamics of the cloud security market forecast from 2022 to 2032 to identify the prevailing market opportunities.
Market research is offered along with information related to key drivers, restraints, and opportunities of cloud security market outlook.
Porter's five forces analysis highlights the potency of buyers and suppliers to enable stakeholders to make profit-oriented business decisions and strengthen their supplier-buyer network.
In-depth analysis of the market segmentation assists in determining the prevailing cloud security market opportunity.
Major countries in each region are mapped according to their revenue contribution to the global market.
Market player positioning facilitates benchmarking and provides a clear understanding of the present position of the market players.
The report includes an analysis of the regional as well as global cloud security market trends, key players, market segments, application areas, and market growth strategies.
Cloud Security Market Report Highlights
| Aspects | Details |
| Market Size By 2032 | USD 125.8 billion |
| Growth Rate | CAGR of 13.6% |
| Forecast period | 2022 - 2032 |
| Report Pages | 495 |
| By Type |
|
| By Enterprise Size |
|
| By Deployment Mode |
|
| By Industry Vertical |
|
| By Region |
|
| Key Market Players | Cloudflare Inc., Broadcom Corporation, Cisco Systems Inc., Trend Micro Inc., IBM Corporation, Tenable Inc., Sophos Ltd., WatchGuard Technologies Inc., Fortinet Inc., BMC Software Inc. |
Analyst Review
As per the insights of the top-level CXOs, the adoption of cloud security technology has a profound impact on the ICT sector revolutionizing various aspects of the industry. Cloud security technology provides 24 x7 visibility by providing continuous visibility to risk posture and its business. The technology helps in handling traffic in an efficient manner through built-in redundancies. In addition, the technology provides data security by design. Furthermore, Cloud storage services help businesses to hold enormous volumes of data eliminating the use of hardware, reducing purchasing expenditure and maintaining servers. The solution also offers automated and regular back-up data thus ensuring data protection and data recovery. Moreover, cloud services can adjust to demand, thus enabling companies to pay only for the resources they utilize. Healthcare professionals use cloud security technology to ensure patient data is handled safely and securely. Government sectors are using cloud security technology to deal with natural disasters and calamities. E-learning platforms use cloud security technology to support their data infrastructure so that simultaneously they can deliver large volumes of educational content to the learners in a safe manner.
The CXOs further added that market players are adopting strategies like geographical expansion to enhance their services in the market and improve customer satisfaction. For instance, in August 2021, Trend Micro Inc. launched cloud one regional data center in India to uphold data sovereignty and safeguard data privacy in the country. Cloud One is Trend Micro flagship cloud security services platform for protecting servers, resources, and applications in the cloud. Some companies used expansion strategies to increase their hold in the cloud security field. For instance, in October 2023, IBM Corporation expanded their IBM cloud security and compliance center, a suite of modernized cloud solutions to assist businesses with risk mitigation and data protection across their workloads and hybrid, and multi cloud systems. Therefore, such strategies are expected to boost the growth of the cloud security market in the upcoming years.
The key players profiled in the cloud security market are Fortinet Inc., Sophos Ltd., Cloudflare Inc., Tenable Inc., BMC Software Inc., Broadcom Corporation, Cisco Systems Inc., IBM Corporation, Trend Micro Inc., and Watchguard Technologies Inc. These players have adopted various strategies to increase their market penetration and strengthen their position in the cloud security market.
The global cloud security market size was valued at $35.8 billion in 2022, and is projected to reach $125.8 billion by 2032
The cloud security market is projected to grow at a compound annual growth rate of 13.6% from 2023 to 2032.
The key players that operate in the cloud gaming market such as Fortinet Inc., Sophos Ltd., Cloudflare Inc., Tenable Inc., BMC Software Inc., Broadcom Corporation, Cisco Systems Inc., IBM Corporation, Trend Micro Inc., and Watchguard Technologies Inc. are the top companies to hold the market share in Cloud Security.
North America is the largest regional market for Cloud Security.
The growing emergence of development security operations in the cloud environment, increasing number of cyber-attacks, growing reliance on cloud-based services, and increasing market for managed services, as these factors propel the growth of cloud security market. Factors such as the development of cloud computing landscape and growth of mobile computing are providing an opportunity for cloud security industry expansion.
Loading Table Of Content...
Loading Research Methodology...



