Security Appliances Market Insights:
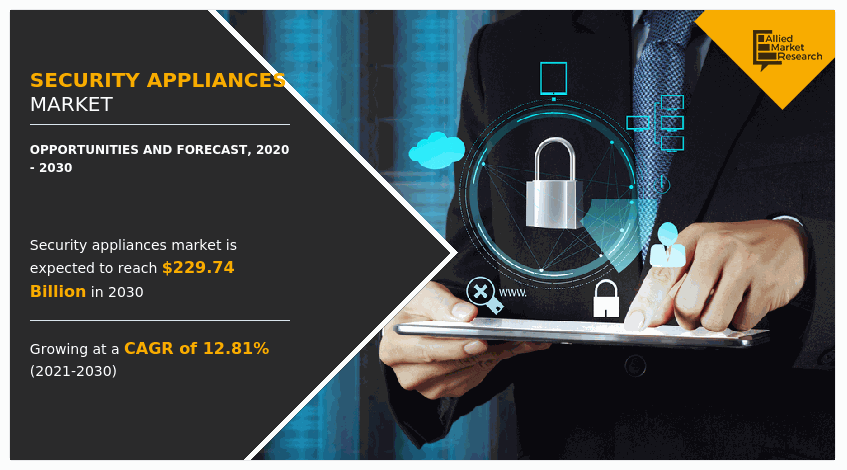
The global security appliances market was valued at $69.18 billion in 2020 and is projected to reach $229.74 billion by 2030, growing at a CAGR of 12.81% from 2021 to 2030.
Increased complexities in network infrastructure are causing a major hindrance in data security management. As a result of these circumstances, outsourcing network security to the security appliance service providers has emerged as a lucrative option for organizations. Also, network security services can be delivered either by setting up necessary security infrastructure or by complete control of the service provider from a remote location
Security appliances incorporate a comprehensive range of practices, tools, and techniques interrelated closely to information and operational technology security. This method uses preventive and responsive methods to defend networks and information from being attacked and compromised. Moreover, security appliances utilize web filtering, legacy malware protection, and advanced threat defense to defend users from Internet-borne threats and to help enterprises enforce Internet policy compliance. The task of information security is becoming more complex with the growth of businesses in terms of size, structure, and utilization of mobile devices, social media, cloud services, and big data. The rising number of security attacks and malicious practices by trained cybercriminal groups have been creating concerns for organizations across all industry sectors.
The global security appliances market share is influenced by a number of factors including increasing cybercrime activities, rising bring-your-own-device implementation, increased demand for cloud-based solutions, and stringent government regulations. Factors such as the need for better security management have impacted both developed and developing economies to protect themselves from unknown entities such as cyber-attack, rivalry, or other disturbing activities. Moreover, the increasing adoption of cloud-based mobile applications boosts the growth of the security appliances market globally. All these factors collectively create opportunities for security appliances market growth, however, some of them account for limitations in the market. However, each factor would have its definite impact on the market
The security appliances market is segmented into By Deployment, By Industry Vertical, and By Type. Based on type, the market is segmented into the firewall, intrusion detection and prevention (IDP), content management, unified threat management (UTM), and virtual private network (VPN). By industry vertical, it is segregated into banking, financial services & insurance (BFSI), public sector, energy & utilities, retail, IT & telecom, manufacturing, aerospace & defense, healthcare, and others. BY Deployment mode, it is bifurcated into cloud-based and on-premise deployment. Region-wise, it is analyzed across North America, Europe, Asia-Pacific, and LAMEA.
On the basis of type, the content management segment dominated the overall security appliances industry in 2020, and is expected to continue this trend throughout the forecast period. The increased threat to corporate networks and information has created a demand for various solutions to protect the network and information. The rise in content data among end-user industries and the increased complexity associated with crucial data has fueled the growth of this segment. Content management users need to integrate data among all business processes, which has resulted in an increased need for robust security to block unauthorized access and data breach.
By Type
The unified threat management (UTM) segment is expected to witness highest growth during the forecast period.
However, the Unified threat management (UTM) segment is expected to grow the most, and this trend is expected to continue during the forecast period. UTM solution enables IT, administrators, to monitor and manage a wide variety of security-related applications and infrastructure components through a single management console. Key features included in UTM are identity-based access control, load balancing, intrusion prevention, and application alertness.
For instance, WatchGuard’s UTM solution is considered a robust solution with functionalities such as application control, intrusion prevention service, web security, and data loss prevention. This solution can streamline network infrastructure while delivering top-rated protection. In the current scenario, the growth of UTM is enhanced due to the rise of mobile devices and remote workers, as well as an explosion of connected devices, encouraging organizations to invest in a reliable cyber security solution. Due to such advanced and reliable features, it would drive the security appliances market growth.
Depending on the industry vertical, Banking, financial services, and insurance (BFSI) segment captured the largest share in 2020 and it will continue this trend during the forecast period. The increasing incidence of cyber-attacks has eroded the trust of consumers in financial institutions, which is one of the major driving factors of the security appliances market. Furthermore, the need to provide sealed security and digital privacy is necessary for financial institutions, as banks and financial institutions intend to take advantage of the cloud, mobile, and social technologies to ensure effective financial management. This in turn is driving the market for security appliances in the BFSI sector.
By Industry Vertical
The healthcare segment is expected to witness the highest growth in the upcoming years.
However, the healthcare segment is expected to witness the highest growth in the upcoming years. The demand for security appliances is constantly increasing in the healthcare industry, as the security of healthcare systems can directly influence operational safety and productivity of the industry, and indirectly impact the services. Furthermore, the frequency and complexity of cyber-attacks have increased in the healthcare industry. In addition, the safety, security, and reliability of data are of utmost importance for these organizations, as they need to ensure compliance with several regulatory requirements related to the documentation and protection of intellectual property which will drive the security appliances market globally.
Depending on the deployment model, the on-premise segment garnered the largest share in 2020 and is expected to continue this trend during the forecast period. This is attributed to numerous benefits provided by this on-premise deployment such as a high level of data security and safety. On-premise deployment model enables installation of the software and permits applications to run on systems present in the premises of the organization, rather than at a distant facility such as server space or cloud. This model is appropriate for specific applications such as financial applications and health records with critical data that entail large data transfers and operations.
By Deployment
The on-premise segment garnered the largest revenue in 2020, and it is expected to continue this trend during the forecast period.
However, the cloud segment is expected to witness the highest growth in the upcoming years. As cloud deployment does not need any investment in IT infrastructure as all data is stored on a cloud server, which increases the demand for security appliances software in small and medium scale organizations. Cloud-based deployment is an application licensing and delivery model, where a vendor or a service provider hosts applications remotely. This deployment model provides the IT team with a greater prospect to facilitate real business value to the organization through lower expected costs and an improved ability to focus on innovation and differentiation
On the basis of region, North America has dominated the overall security appliances industry in 2020 and is expected to continue this trend throughout the forecast period. Owing to the high adoption of technology, a large number of security appliances market players, and innovative solutions. In addition, factor such as the shift of work towards remote working and increasing attack of external threats increases the use of security appliances in this region, which provides lucrative growth opportunities for this region. However, The Asia-Pacific is expected to exhibit the highest growth during the forecast period, owing to strong economic growth along with the ongoing development in security appliances and inventory management, which drives the organizations to invest heavily in the security appliances market to sustain growth and improve productivity.
In addition, factors such as major shift toward digital transformation, cloud deployment & technological advancement among small & medium businesses, and continuously ongoing modernization in workforce management strategy in emerging economies notably contribute toward the market growth. Furthermore, key players in Asia-Pacific are focusing on enhancing their operations and increasing their overall efficiency to stay competitive in the security appliances market, which is expected to provide lucrative opportunities for the growth of the market during the forecast period.
Top Impacting Factors:
The global security appliances market is influenced by a number of factors including increasing cybercrime activities, rising bring-your-own-device implementation, increased demand for cloud-based solutions, and stringent government regulations. Factors such as the need for better security management have impacted both developed and developing economies to protect themselves from unknown entities such as cyber-attack, rivalry, or other disturbing activities. Moreover, the increasing adoption of cloud-based mobile applications boosts the growth of the market globally. All these factors collectively create opportunities for market growth, however, some of them account for limitations in the security appliances market. However, each factor would have its definite impact on the market.
Increasing cybercrime activities
Today, cyber-attacks, which are mainly driven by skilled professional hackers and organized criminal groups, are growing at a rapid pace. The financial costs incurred due to data breaches are also increasing with the complexity of attacks. However, the aggregate impact of cybercrime on businesses is unknown, even small attacks such as viruses and worms cause billions of dollars of financial loss each year. Therefore, organizations/companies need cost-effective and efficient mechanisms to protect sensitive information from phishing, web hacking, hacktivism, and cyber espionage.
Recently, publicly engineered phishing emails along with other email attacks were a major concern. These attacks are expected to continue due to growth in Internet reliability and an increase in usage of mobile devices in the corporate environment. Furthermore, phishing attacks are one of the most common security challenges faced by organizations that enable access to passwords, credit card information, and other sensitive information regarding phone calls, emails, and social media accounts.
Competition Analysis:
Competitive analysis and profiles of the major players in the security appliances market include Cisco Systems, Inc., Check Point Software Technologies Ltd., Symantec Corporation, Intel Corporation, Fortinet, Inc., Palo Alto Networks, Inc., Bosch Sicherheitssysteme GmbH, Honeywell International Inc., Johnson Controls International plc. and Juniper Networks, Inc.
Key Benefits for Stakeholders:
- This report provides a quantitative analysis of the market segments, current trends, estimations, and dynamics of the security appliances market analysis from 2020 to 2030 to identify the prevailing security appliances market opportunities.
- The security appliances market research is offered along with information related to key drivers, restraints, and opportunities.
- Porter's five forces analysis highlights the potency of buyers and suppliers to enable stakeholders make profit-oriented business decisions and strengthen their supplier-buyer network.
- In-depth analysis of the security appliances market segmentation assists to determine the prevailing market opportunities.
- Major countries in each region are mapped according to their revenue contribution to the global market.
- Market player positioning facilitates benchmarking and provides a clear understanding of the present position of the market players.
- The report includes the analysis of the regional as well as global security appliances market trends, key players, market segments, application areas, and market growth strategies.
Security Appliances Market Report Highlights
| Aspects | Details |
| By Deployment |
|
| By Industry Vertical |
|
| By Type |
|
| By Region |
|
| Key Market Players | SYMANTEC CORPORATION, INTEL CORPORATION, BOSCH SICHERHEITSSYSTEME GMBH, CHECK POINT SOFTWARE TECHNOLOGIES LTD., HONEYWELL INTERNATIONAL INC., FORTINET, INC., Trend Micro Inc, CISCO SYSTEMS, INC., PALO ALTO NETWORKS, INC., JUNIPER NETWORKS, INC. |
Analyst Review
According to CXOs of leading companies, the security appliances market indicates a favorable scenario for the software and services industry. The current business scenario has witnessed an increase in the adoption of security appliances in developed as well as developing regions. This growth is attributed to technological innovation in product offerings, increase in application areas among end-use industries, and heavy venture capital investments in R&D activities to develop solutions with enhanced capabilities. Rising number of security breaches and government regulations regarding IT security are expected to stimulate organizations/companies to enhance their data security infrastructure. The outsourcing of IT security services is estimated to continue during the forecast period due to cost advantages for end-use industries and shortage of skilled IT resources, which is expected to support the market growth.
Furthermore, industry players are constantly developing advanced solutions to meet customer demand. Different industry verticals are facing advanced attacks on their IT networks. The BFSI sector is continuously experiencing cyber-attacks from different entities including hackers and cyber criminals that are forcing them to enhance the security of their IT networks. BFSI, telecom and IT sectors are expected to have a major share in the overall market. Among the different regions, North America is expected to dominate the global market, while Asia-Pacific is estimated to exhibit the highest growth rate due to high growth among industry verticals from developing nations in this region. On the other hand, LAMEA is expected to grow at a significant rate, predicting a lucrative market growth for security solutions, especially in countries such as Brazil, South Africa, and Argentina.
Nevertheless, prominent market players are exploring new technologies and applications to meet the increase in customer demands. Product launches, collaborations, and acquisitions are expected to enable them to expand their product portfolios and penetrate different regions. Emerging economies provide lucrative opportunities to market players for growth.
The global security appliances market size was valued at $69.18 billion in 2020 and is projected to reach $229.74 billion by 2030
The global security appliances market is expected to grow at a compound annual growth rate (CAGR) of 12.81% from 2020-2030 to reach $229.74 billion by 2030
Major key players in the security appliances market research report include Cisco Systems, Inc., Check Point Software Technologies Ltd., Symantec Corporation, Intel Corporation, Fortinet, Inc., Palo Alto Networks, Inc., Bosch Sicherheitssysteme GmbH, Honeywell International Inc., Johnson Controls International plc. and Juniper Networks, Inc.
The Asia-Pacific is expected to exhibit the highest growth during the forecast period
The need for better security management have impacted both developed and developing economies to protect themselves from unknown entities such as cyber-attack, rivalry, or other disturbing activities. Moreover, the increasing adoption of cloud-based mobile applications boosts the growth of the market globally.
Loading Table Of Content...



